You complete an IT audit. You review the report. You see charts, risk scores, and a list of findings. For a moment, you feel reassured because you have documentation showing that someone reviewed your systems.
But weeks later, daily operations feel the same. Your internal IT team still feels stretched. Leadership still asks for clarity about risk. When a new insurance form or vendor questionnaire arrives, you scramble again to gather evidence.
The issue is not that audits lack value. The issue is how most organizations interpret them. Traditional audits often miss the bigger governance picture. They show what exists, but they rarely show who owns it, how decisions get made, or where risk is building.
If you treat an IT audit as a snapshot instead of a signal, you miss the full story.
The False Confidence That Follows an IT Audit
A standard IT audit reviews documented policies, system settings, and technical controls. It looks at password rules, backup status, patch levels, and access permissions. It confirms that tools are installed and policies are written.
That information matters. You need to know that multifactor authentication is enabled, backups run on schedule, antivirus updates are applied correctly, and users receive security training.
However, what the audit does not measure is just as important. It does not clearly define who owns each control every day. It does not show how quickly your team fixes gaps. It does not explain how budget delays or unclear decision authority increase risk. It also rarely highlights tension between internal IT and your managed service provider.
If you operate with 25 to 500 users, complexity increases quickly. You add applications, remote staff, vendors, and compliance requirements. Each change introduces new risk. A once-a-year IT audit cannot capture the daily reality of that growth. You should treat it as a starting point, not a finish line.
Where Governance Structure Matters Most in Co-Managed IT
Co-managed IT strengthens organizations by combining internal knowledge with external expertise. It increases capability, resilience, and strategic alignment.
To unlock that value fully, ownership and accountability must be clearly defined.
Risk increases when ownership is not clearly documented and reinforced through governance processes.
Without documented responsibility matrices, assumptions can form around patching, backup monitoring, identity management, vendor oversight, and endpoint security.
Tools may overlap. Processes may differ. Standards may not always be aligned.
These gaps often do not appear in an IT audit report. The report may confirm that a control exists and works during testing. It does not show who ensures it remains effective over time. As a result, visibility becomes fragmented. Each party sees part of the environment, but no one sees the whole picture.
Compliance Checklists Do Not Equal Governance
Compliance focuses on meeting requirements. Governance focuses on ownership, decisions, and accountability.
When you treat an IT audit as a compliance exercise, you ask:
- Is MFA enabled?
- Is there a written security policy?
- Are backups running?
These are good questions. Governance asks deeper ones:
- Who ensures MFA stays enforced as new systems are added?
- Who updates policies when business operations change?
- Who tests backups and reports results to leadership?
Checklist compliance confirms that controls exist. Governance ensures they stay effective.
Decision delays often weaken strong controls. You may identify a firewall upgrade as urgent, but it sits in a report for months because leadership does not fully understand the risk. Budget approval may require repeated discussions without clear ownership.
When findings are acknowledged but not assigned, they fade into the background. Over time, your risk increases, even if your documentation looks complete.
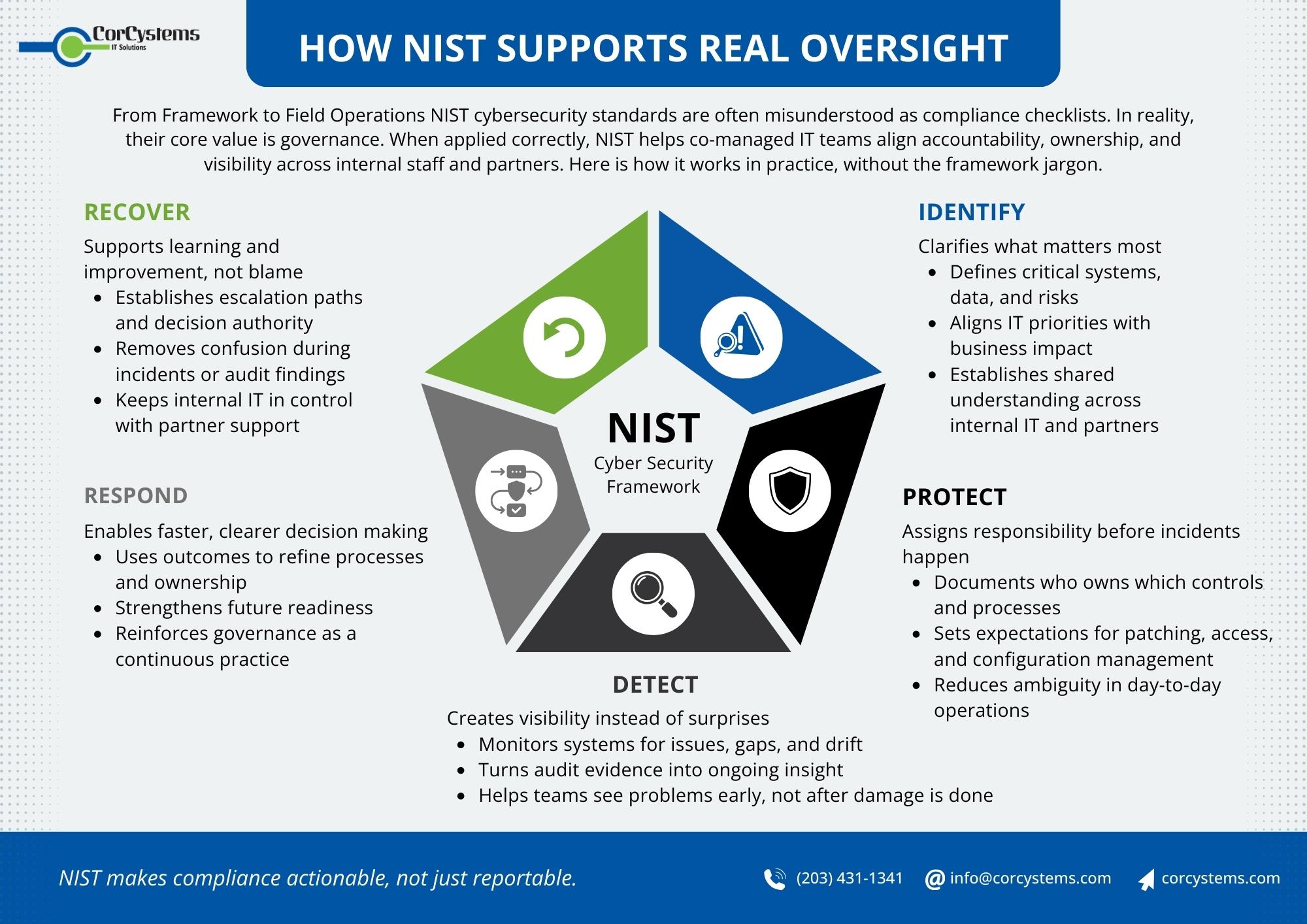
How NIST Cybersecurity Standards Change the Conversation
Structured frameworks help close this gap. NIST cybersecurity standards provide a clear way to organize security and risk efforts.
The NIST framework includes five core functions: Identify, Protect, Detect, Respond, and Recover. These categories move you beyond individual tools and toward structured risk management.
- Identify means understanding your assets, data, and risks.
- Protect includes safeguards such as access controls and awareness training.
- Detect focuses on monitoring and alerts.
- Respond covers incident handling.
- Recover supports business continuity.
When you align your controls with NIST cybersecurity standards, you shift the conversation. Instead of asking only, “Do we have antivirus?” you ask, “How does this control reduce risk, and who ensures it works?”
NIST 2.0 compliance strengthens this approach. It ties cybersecurity more closely to overall business risk and highlights leadership accountability. It makes governance a core part of security strategy, not an afterthought.
What Meaningful Oversight Looks Like in Practice
Strong oversight shows up in clear ways across your organization.
Defined Control Ownership
Each critical control has documented ownership. Your internal IT manager knows what remains in-house and what belongs to your MSP. Your external partner has access to the tools and data needed to support security properly.
Context-Driven Reporting
Dashboards provide context, not just numbers. Reports explain why a risk matters, what action is underway, and who is responsible. Escalation paths are clear. If a control fails, everyone knows who responds and who informs leadership.
Strategy-Aligned Reviews
Quarterly reviews connect technical findings to business goals. Budget discussions reflect real risk data. Investment decisions focus on reducing exposure, not reacting to isolated issues.
Active Executive Involvement
Executive leadership takes part in security planning because they understand that oversight protects business continuity and client trust. Governance becomes a shared responsibility, not just an IT task.
Confident Operational Execution
Internal IT works with clarity about authority and budget support. External partners provide validation, strategy, and alignment with frameworks such as NIST CSF.
Organizations that apply governance intentionally within a co-managed IT structure reduce friction and increase performance. Shared visibility strengthens trust. Clear ownership accelerates decisions. Instead of reacting to audit findings, teams operate from a shared operating model.
CorCystems has seen this improvement among co-managed clients who commit to defined processes and responsibilities. The result is stronger accountability that supports steady business growth.
Questions to Ask After Your Next IT Audit
When your next report arrives, pause before filing it away. Ask:
- Who owns each remediation item by name?
- What business risk ties to each finding?
- Which decisions require executive approval?
- How do our controls align with NIST cybersecurity standards?
- Are we progressing toward NIST 2.0 compliance in a structured way?
- Do we have support through IT compliance consulting or compliance as a service to maintain momentum?
- What will change in the next 90 days because of this review?
These questions shift the focus from documentation to responsibility. They move the conversation to the leadership level.
Building Oversight That Matches Your Growth
As your organization grows, your IT environment grows with it. More users, more applications, more vendors, and more expectations increase complexity. You cannot manage that complexity through annual reports alone.
An IT audit provides visibility. Governance creates control. Shared environments require shared accountability supported by structure.
In a well-governed co-managed IT environment, audits become operational signals that guide action, not isolated compliance exercises.
If you rely only on checklists, you will continue reacting to gaps. If you align your environment with NIST cybersecurity standards, pursue NIST 2.0 compliance thoughtfully, and use IT compliance consulting or compliance as a service to maintain oversight, you create operational clarity.
If you would like a practical discussion about strengthening oversight and closing accountability gaps, schedule a strategy conversation with our team today.