
Empowering Healthcare: The Strategic Impact of MSPs
For healthcare providers, the delicate balance between robust data security and exceptional patient care is paramount. Electronic health records (EHRs) hold a wealth of

For healthcare providers, the delicate balance between robust data security and exceptional patient care is paramount. Electronic health records (EHRs) hold a wealth of

Are you confident your business can thrive in the face of rapid technological advancements? If not, you’re not alone. Many businesses struggle to keep

In today’s hyper-connected world, where data is the lifeblood of every business, the stakes for data security and resilience have never been higher. According

In today’s digitally driven world, businesses are bullseyes for cyberattacks, particularly malware. It’s estimated that 300,000 new pieces of malware are created every
The cloud is no longer a novelty; it’s the driving force behind modern business. According to experts, a whopping 60% of business data is

Are co-managed services on your radar this year? As we begin 2024, businesses face a digital landscape full of both daunting challenges and exhilarating
Welcome to the digital age, where technology pulses at the core of every organization, and cybersecurity isn’t just a buzzword – it’s a crucial

Is your business protected from cybersecurity threats? As we enter the new year, the digital landscape will continue to evolve. And, while this

As the reliance on technology for businesses increases, so too does the need to collaborate with Managed Service Providers (MSPs). MSPs are essential for
Introduction to Risk Assessment Best Practices in Cybersecurity As businesses continue to expand their digital footprint, the task of maintaining a secure IT environment

Summer at CorCystems has been nothing short of extraordinary, thanks to the fresh energy and enthusiasm brought in by our interns. Today, we shine
Keeler Tavern Museum & History Center: A Beacon of History Nestled in the heart of Ridgefield, CT, the Keeler Tavern Museum & History Center

Meet Izzy Shaikh, a dedicated member of our team at CorCystems. His passion for technology and helping others has driven his pursuit of a
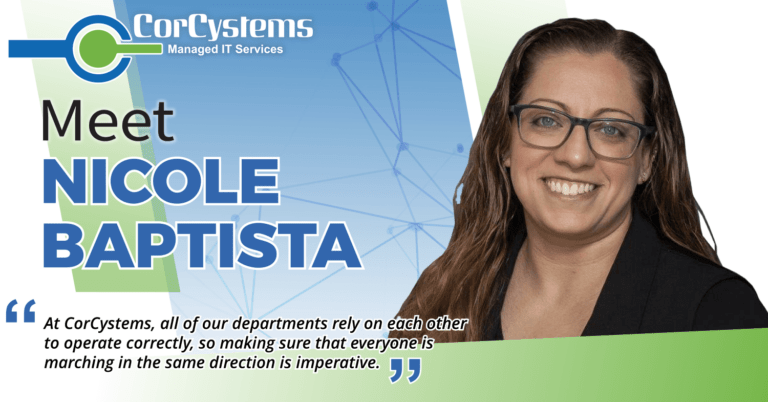
We’re excited to introduce you to Nicole Baptista, the dynamo leading Service Delivery at CorCystems. Combining a passion for technology with her impressive customer
Miller Motorcars: A Leader in Luxury Auto Sales, Fueled by CorCystems IT Support At Miller Motorcars, pursuing perfection is not merely a goal—it’s

We’re excited to put the spotlight on Sabrina Brereton, one of our dedicated accountants at CorCystems. Sabrina discovered her love for accounting after starting

CorCystems understands the importance of ransomware backup solutions for businesses. However, with ransomware attacks on the rise, it is crucial to have a plan
At CorCystems, we’re proud to work with organizations that are making a positive impact in their communities. Today we want to highlight one of

For healthcare providers, the delicate balance

Are you confident your business can

In today’s hyper-connected world, where data